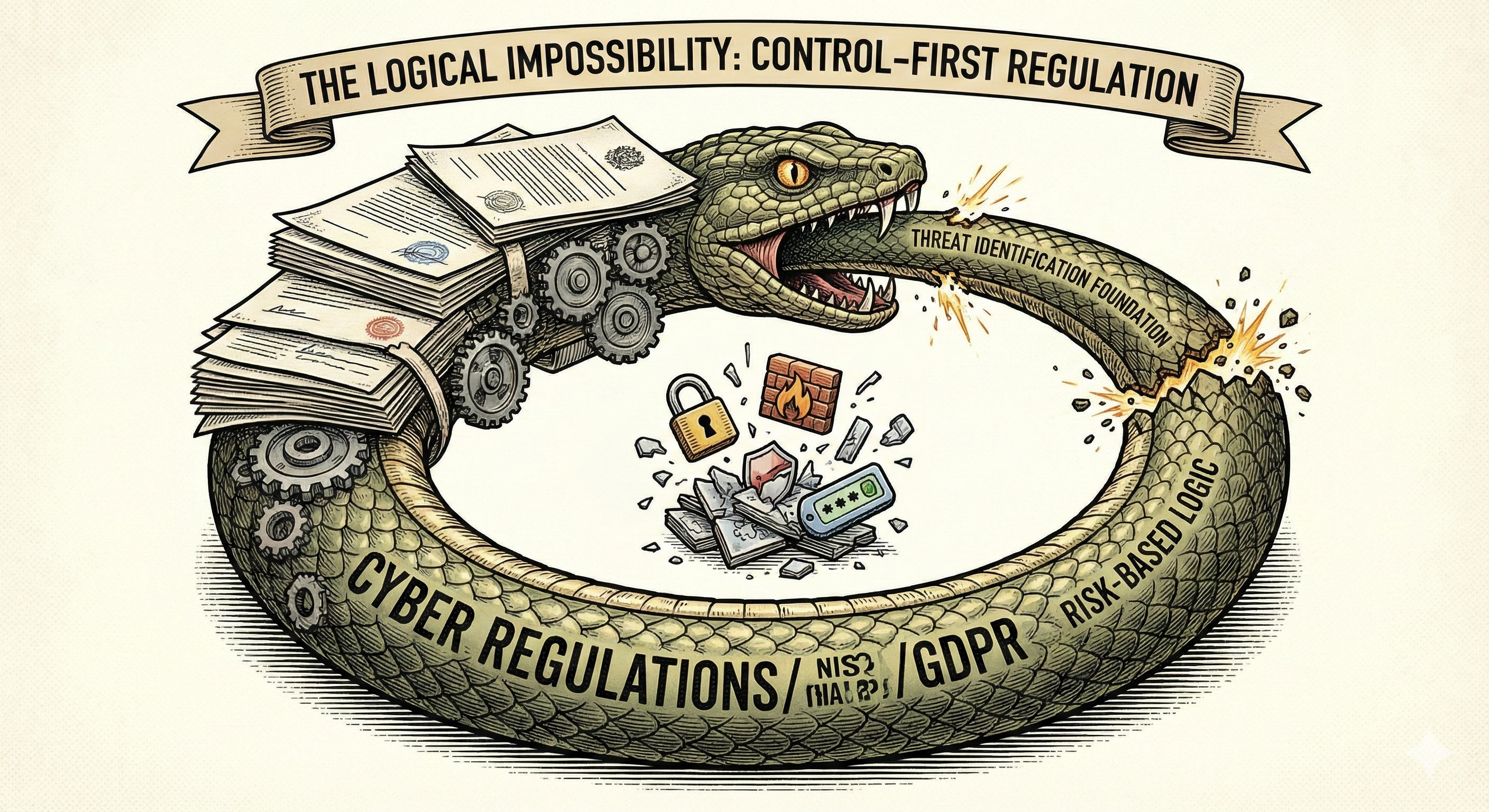
Modern cybersecurity regulations like NIS2 and DORA operate on a control-first premise that contradicts the very standards they cite. By mandating controls without identifying specific threats, they create a logical gap that makes proportionality impossible. This article identifies two missing dimensions in all 30+ major regulations examined—and shows how a cause-oriented taxonomy resolves the paradox.
The Premise Every Regulator Claims
Open any cybersecurity regulation—NIS2, DORA, GDPR Article 32, PCI-DSS, HIPAA Security Rule, or sector-specific frameworks from financial services to critical infrastructure—and you will find the same foundational claim: "These requirements are based on internationally recognized standards."
The standards they reference—ISO/IEC 27001, NIST Cybersecurity Framework, and their derivatives—share a core principle so fundamental it appears in their opening chapters:
This is not merely a recommendation. It is the logical structure that makes control selection defensible. A control exists to address a threat. Without knowing what threat you're addressing, control selection becomes arbitrary.
The Regulatory Reality
Now examine what those same regulations actually require. They mandate specific controls: "Implement encryption." "Establish access controls." "Maintain audit logs." "Conduct penetration testing." "Implement multi-factor authentication."
Notice what is missing. The regulation never states: "Encryption is required because it mitigates Threat X." It never identifies which threat each control addresses. It simply mandates the control and moves on.
The Two Missing Dimensions
This creates not one, but two logical impossibilities. When a regulator mandates Control X as obligatory, they implicitly claim:
- There exists a Threat Y that Control X addresses
- Threat Y is relevant to the regulated entities
- The risk from Threat Y justifies the cost of Control X
- Control X operates at the right point in the attack chain
Yet regulations never state what Threat Y is, nor do they clarify where in the causal chain the control operates. This reveals two missing dimensions:
The Kreinz Thesis
Cybersecurity regulations claim to follow risk-based standards but are missing two essential dimensions that those standards require:
| Dimension | Missing Question | TLCTC Answer |
|---|---|---|
| Horizontal | Which generic vulnerability / threat? | The 10 Clusters (#1–#10) |
| Vertical | Where in the causal chain? | Bow-Tie: Cause-side vs Consequence-side |
Without these two dimensions, regulated entities face impossible questions:
- They cannot verify the logic. They cannot confirm whether Control X actually addresses a threat relevant to their environment.
- Proportionality becomes impossible. Risk-based thinking requires knowing what risk you're addressing.
- Control architecture is incoherent. Preventive and mitigating controls are mixed without acknowledging they serve fundamentally different purposes.
- Compliance replaces security. When you cannot trace a control to a threat, you implement the control to satisfy the auditor and regulator and your compliance risk, not to reduce your cyber risk.
Universal Validation: 30 Regulations, Zero Exceptions
To test whether this was a selective observation or a universal pattern, I examined 30 cybersecurity regulations and standards across four jurisdictions (US, UK, EU, Switzerland) and multiple sectors. The result: every single regulation fails both dimensions.
| Jurisdiction | Regulation | Controls Mandated | Has Threat Taxonomy? | Distinguishes Chain Position? |
|---|---|---|---|---|
| General Cybersecurity Legislation | ||||
| EU | NIS2 Directive | 10+ (Art. 21) incl. MFA, encryption | ❌ | ❌ |
| EU | GDPR Article 32 | Encryption, pseudonymisation, CIA+R | ❌ | ❌ |
| EU | Cyber Resilience Act | 15+ product security (Annex I) | ❌ | ❌ |
| EU | AI Act (Art. 15) | Robustness & cybersecurity for high-risk AI | Partial | ❌ |
| EU | Radio Equipment Directive | Network protection, privacy, fraud | ❌ | ❌ |
| US | FISMA / NIST 800-53 | 1,000+ controls | ❌ | ❌ |
| US | EO 14028 | MFA, Zero Trust, EDR, SBOM | ❌ | ❌ |
| US | CISA BOD 22-01 (KEV) | Specific CVE patching | ❌ | ❌ |
| UK | NIS Regulations 2018 | Outcome-based | ❌ | ❌ |
| UK | UK GDPR Article 32 | Examples only | ❌ | ❌ |
| CH | nDSG Article 8 | Protection goals | ❌ | ❌ |
| Financial Sector Regulations | ||||
| EU | DORA | 50+ across 11 articles | ❌ | ❌ |
| EU/UK | PSD2 RTS on SCA | Strong Customer Auth (2FA) | ❌ | ❌ |
| US | NY DFS Part 500 | MFA, encryption, access controls | ❌ | ❌ |
| US | GLBA Safeguards Rule | MFA, encryption, access controls | ❌ | ❌ |
| US | SEC Regulation S-P | Incident response, access controls | ❌ | ❌ |
| US | FFIEC CAT | Assessment-based | ❌ | ❌ |
| UK | FCA PS21/3 | Outcome-based resilience | ❌ | ❌ |
| UK | PRA SS1/21 | Outcome-based resilience | ❌ | ❌ |
| CH | FINMA Circular 2023/1 | References ISO 27001 | ❌ | ❌ |
| Critical Infrastructure | ||||
| US | NERC CIP | 45+ requirements across CIP-002–014 | ❌ | ❌ |
| US | TSA Pipeline Directive | Segmentation, MFA, patching | ❌ | ❌ |
| US | HIPAA Security Rule | Technical safeguards | ❌ | ❌ |
| US | CMMC 2.0 | 110+ practices (Level 2) | ❌ | ❌ |
| CH | SKI Strategy | References ISO 27001 | ❌ | ❌ |
| Industry Standards | ||||
| Global | PCI-DSS v4.0 | 250+ requirements | ❌ | ❌ |
| Global | ISO 27001:2022 | 93 controls (Annex A) | ❌ | ❌ |
| Global | NIST CSF 2.0 | Process-based | ❌ | Process only |
| Global | SOC 2 | Trust criteria | ❌ | ❌ |
| TOTAL: 30 Regulations Examined | 0 / 30 | 0 / 30 | ||
The pattern is universal. Not a single regulation examined provides a threat taxonomy that would allow controls to be traced to specific threats, and not a single regulation distinguishes between controls that prevent compromise versus controls that limit damage after compromise.
Why Both Dimensions Matter: The MFA vs. Encryption Example
Consider two controls that regulations frequently mandate together: Multi-Factor Authentication (MFA) and Encryption at Rest. Most regulations list them side by side as if they were equivalent security measures. They are not.
| Control | Which Threat? (Horizontal) | Chain Position (Vertical) | Purpose |
|---|---|---|---|
| MFA | #4 Identity Theft | CAUSE-SIDE (Preventive) | Prevents credential compromise from succeeding |
| Encryption at Rest | Data Protection | CONSEQUENCE-SIDE (Mitigating) | Protects data IF system is already compromised |
Without the horizontal dimension, you cannot answer: "Which threat does this control address?" Without the vertical dimension, you cannot answer: "Does this control prevent compromise or limit damage after compromise?" Regulations that conflate these produce incoherent security architectures.
The TLCTC Solution: A Two-Dimensional Framework
The Top Level Cyber Threat Clusters (TLCTC) framework provides exactly the two-dimensional structure that regulations lack, through its Bow-Tie model:
The 10 Threat Clusters (Horizontal Dimension)
TLCTC classifies threats by the generic vulnerability they exploit, not by outcomes:
| Cluster | Generic Vulnerability |
|---|---|
| #1 Abuse of Functions | Designed features enabling unintended actions |
| #2 Exploiting Server | Server-side implementation flaws |
| #3 Exploiting Client | Client-side implementation flaws |
| #4 Identity Theft | Weak identity/credential management |
| #5 Man in the Middle | Unprotected communication paths |
| #6 Flooding Attack | Finite capacity resources |
| #7 Malware Execution | Designed execution capability |
| #8 Physical Attack | Physical accessibility |
| #9 Social Engineering | Human psychological factors |
| #10 Supply Chain Attack | Third-party trust dependencies |
The Causal Chain (Vertical Dimension)
The Bow-Tie model separates controls by their position in the attack chain:
| Position | Purpose | Example Controls | NIST CSF |
|---|---|---|---|
| Cause-Side (Preventive) | Prevent system compromise | MFA, patching, input validation, access controls | IDENTIFY, PROTECT |
| Central Event | Detect compromise occurred | SIEM alerts, anomaly detection, EDR | DETECT |
| Consequence-Side (Mitigating) | Limit damage after compromise | Encryption at rest, backup/recovery, segmentation | RESPOND, RECOVER |
What Coherent Regulation Would Look Like
With this two-dimensional structure, a regulatory requirement could finally be stated coherently:
"Organizations shall implement controls addressing #4 Identity Theft, specifically multi-factor authentication for privileged access, because weak credential management enables unauthorized system access. This is a cause-side preventive control."
This statement identifies the threat (#4), names the generic vulnerability (weak credential management), specifies the control (MFA for privileged access), explains the causal relationship, and positions the control in the attack chain. It can be verified, challenged, and proportionally assessed.
Conclusion
The logical flaw in cybersecurity regulation is not subtle. It is a structural contradiction between what the referenced standards require (identification-first, chain-aware) and what the regulations themselves do (control-first without identification or chain positioning).
This contradiction cannot be resolved by writing more detailed control requirements. It can only be resolved by doing what the standards have always demanded: identifying threats first across both dimensions—which threat and where in the chain—then deriving control requirements from that identification.
The TLCTC framework provides the missing structure. It's available under CC BY 4.0 at tlctc.net.
Appendix: Detailed Regulation Analysis
This appendix provides detailed analysis of selected regulations, demonstrating how each conflates cause-side and consequence-side controls in flat lists without threat taxonomy.
EU GDPR Article 32 — Security of Processing
Structure: (a) pseudonymisation and encryption; (b) CIA of systems; (c) restore availability; (d) testing.
| Requirement | Chain Position | Protects Against |
|---|---|---|
| (a) Pseudonymisation | Consequence-side | Data exposure AFTER compromise |
| (a) Encryption | Mixed | Transit=cause-side, Rest=consequence-side |
| (b) CIA of systems | Cause-side | System compromise |
| (c) Restore availability | Consequence-side | After incident |
| (d) Testing | Meta-control | Both |
Verdict: Flat list mixing cause-side and consequence-side controls without distinction.
US HIPAA Security Rule — §164.312 Technical Safeguards
Structure: (1) Access Control, (2) Audit Controls, (3) Integrity, (4) Authentication, (5) Transmission Security.
| Safeguard | Chain Position | Purpose |
|---|---|---|
| Unique user ID | Cause-side | Prevent unauthorized access |
| Automatic logoff | Cause-side | Limit exposure window |
| Encryption/decryption | Consequence-side | Protect data if accessed |
| Audit controls | Detection | Identify compromise |
| Person authentication | Cause-side | Prevent Identity Theft (#4) |
| Transmission encryption | Cause-side | Prevent interception (#5) |
The Conflation: "Encryption and decryption" is listed under "Access Control" alongside "Unique user identification"—but User ID prevents unauthorized system access; Encryption protects data IF unauthorized access occurs.
Verdict: Flat list with superficial categorization. No cause-consequence distinction.
US NIST 800-53 Rev 5
Structure: 20 control families, 1,000+ controls.
| Family | Controls | Chain Position |
|---|---|---|
| AC (Access Control) | 25 controls | Mostly cause-side |
| AU (Audit & Accountability) | 16 controls | Detection |
| CP (Contingency Planning) | 13 controls | Consequence-side |
| IR (Incident Response) | 10 controls | Consequence-side |
| SC (System & Communications) | 51 controls | Mixed |
The Problem with SC (System & Communications): SC-8 (Transmission Confidentiality) is cause-side; SC-28 (Protection at Rest) is consequence-side. Both in same family with no distinction.
Verdict: Extensive controls, no chain positioning. Baselines based on impact levels, not on whether controls prevent compromise vs. protect data after compromise.
Research conducted December 2025 across US, UK, EU, and Swiss jurisdictions.
