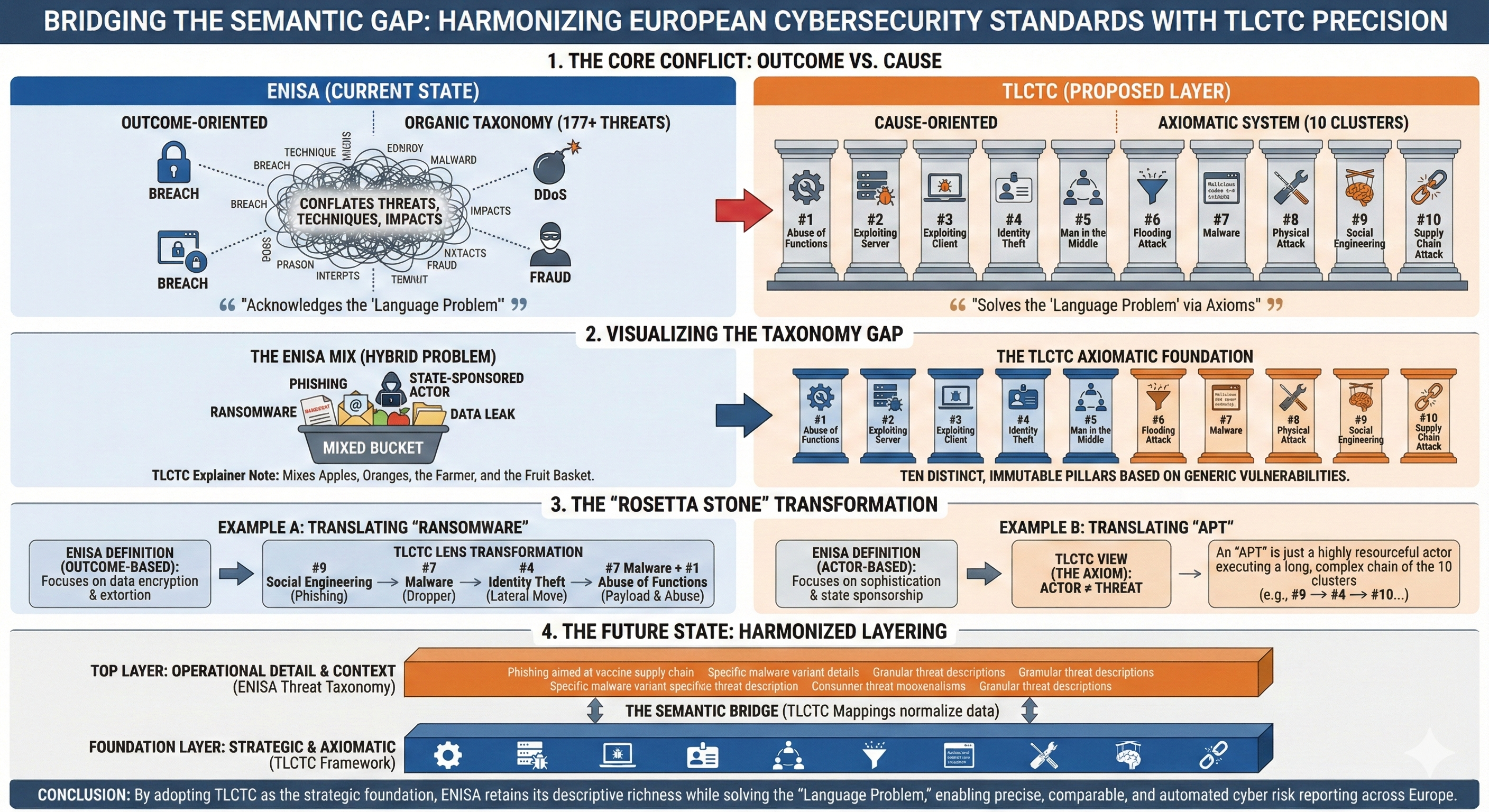
This analysis examines how the European Union Agency for Cybersecurity (ENISA) addresses cyber risk and cyber threat definitions, identifying structural gaps in their current framework that the Top Level Cyber Threat Clusters (TLCTC) framework could address. ENISA operates with a hybrid classification approach that is predominantly outcome-based rather than cause-oriented, creating significant conceptual conflation between threats, techniques, and impacts. The TLCTC framework, with its cause-oriented, actor-agnostic taxonomy based on 10 non-overlapping generic vulnerabilities, directly addresses this foundational deficit.
Part I: ENISA's Current Approach to Cyber Threats and Risk
1.1 ENISA's Foundational Threat Definition
ENISA's foundational definition of cyber threat comes from their 2016 Threat Taxonomy: "Cyber Threats should be understood as threats applying to assets related to information and communication technology." The definition further specifies that such threats are materialized mostly in cyberspace, while some threats included are materialized in the physical world but affect information and cyber-assets.
This broad scoping creates immediate boundary challenges—physical sabotage of network infrastructure sits alongside software vulnerabilities in the same framework, without clear differentiation of the generic vulnerability being exploited.
1.2 The Nine-Category ENISA Threat Taxonomy
The ENISA Threat Taxonomy (Version 1.0, January 2016, updated 2022) organizes threats into nine high-level categories containing 177 detailed threats:
| # | Category | Examples |
|---|---|---|
| 1 | Physical Attack (Deliberate) | Fraud, sabotage, vandalism, theft, terrorism |
| 2 | Unintentional Damage | Human errors, accidental leaks, configuration mistakes |
| 3 | Disaster (Natural) | Earthquakes, floods, fires, radiation leaks |
| 4 | Failures/Malfunctions | Equipment failures, communication disruptions |
| 5 | Outages | Personnel absence, internet/network outages |
| 6 | Eavesdropping/Hijacking | Espionage, man-in-the-middle attacks |
| 7 | Nefarious Activity/Abuse | Malware, DDoS, social engineering, ransomware, APTs |
| 8 | Legal | Regulatory violations, contractual failures |
| 9 | Information Manipulation | Disinformation campaigns (added post-2016) |
1.3 The ETL Prime Threats: Outcome-Oriented Classification
The annual ENISA Threat Landscape (ETL) reports use a simplified seven-threat framework for strategic communication. This structure reveals ENISA's predominantly outcome-based approach:
| Prime Threat | Classification Nature (Problem) |
|---|---|
| Ransomware | Attack type + business model + outcome conflated |
| Malware | Tool category (overlaps with ransomware) |
| Social Engineering | Attack methodology spanning multiple stages |
| Threats Against Data | Outcome category (data breach/leak) — not a cause |
| Threats Against Availability | Attack technique + outcome conflated |
| Information Manipulation | Campaign type + outcome |
| Supply Chain Attacks | Vector category (closest to cause-based) |
A ransomware attack delivered via phishing that causes data exfiltration could legitimately appear under ransomware, malware, social engineering, AND threats against data. The extent of this issue is visible in the ETL 2025 report, which analyzed 4,875 incidents where DDoS comprised 76.7% of incidents—skewing the landscape due to classification overlaps.
1.4 ENISA's Risk Framework Approach
ENISA's risk definition follows standard formulations: Risk = Likelihood × Impact, extended per ISO 27005 as Risk = Impact × Threat Likelihood × Vulnerability Level. However, a critical finding from their 2022 Compendium of Risk Management Frameworks is that ENISA does not incorporate Bow-Tie analysis or explicit cause-consequence separation in their core methodologies.
1.5 ENISA's Acknowledged 'Language Problem'
A 2015 ENISA publication titled 'Definition of Cybersecurity – Gaps and overlaps in standardisation' directly confronts terminological chaos:
"Finding a common understanding is a major challenge and it might not be possible to harmonize the definition and usage of the term."
ENISA documented how even the spelling (Cybersecurity vs. cyber security vs. Cyber Security) lacks consensus across international bodies. Furthermore, the ETL methodology contains extensive caveats acknowledging that 28.5% of incidents in ETL 2025 lacked sector classification.
Part II: Identified Gaps in ENISA's Current Framework
2.1 Structural Conflation Problems
The most significant gap is mixing conceptual levels without clear methodological justification. Their prime threat categories conflate:
- Root causes (vulnerability exploited) with attack mechanisms (technique used).
- Tools (malware) with specific malware types (ransomware listed separately).
- Techniques (social engineering) with outcomes (threats against data).
- Actor motivations with threat categories (ENISA's ETL 2018 acknowledged 'cyber espionage' is 'more a motive than a cyberthreat').
2.2 Absence of Cause-Based Classification
ENISA's taxonomy was developed as an "internal structuring aid for information collection" that "emerged organically over 2012-2015 rather than through systematic design." The framework currently lacks:
- Explicit generic vulnerability identification for each threat category.
- Non-overlapping classification criteria (mutual exclusivity).
- Attack path sequencing capability (attack steps as ordered sequences).
- Velocity analysis for control effectiveness assessment.
- Domain boundary crossing notation.
2.3 No Native Bow-Tie Integration
ENISA's ISO 27005-aligned approach treats cause-consequence distinction as implicit rather than explicit. This creates challenges for control mapping (preventive vs. mitigating), risk register development, and business impact analysis that doesn't conflate threat type with outcome type.
2.4 Incomplete Harmonization Despite Significant Investment
ENISA's harmonization efforts remain structurally incomplete. The Reference Incident Classification Taxonomy (RSIT) itself is described as "an adaptation of the CERT.PT taxonomy, which in turn is based on the eCSIRT.net mkVI taxonomy"—demonstrating ongoing fragmentation rather than convergence. Significantly, the 2025 CTL Methodology notes that the ENISA threat taxonomy is "currently under revision for the purpose of developing a more mature, actionable framework."
Part III: How TLCTC Addresses ENISA's Gaps
3.1 TLCTC's Cause-Oriented Architecture
The Top Level Cyber Threat Clusters framework provides exactly what ENISA's current approach lacks: a cause-oriented, actor-agnostic taxonomy that classifies threats by the generic vulnerability initially exploited.
| # | TLCTC Cluster | Generic Vulnerability Exploited |
|---|---|---|
| 1 | Abuse of Functions | Legitimate functionality misused beyond intended scope |
| 2 | Exploiting Server | Implementation flaw in server-role component |
| 3 | Exploiting Client | Implementation flaw in client-role component |
| 4 | Identity Theft | Compromise of identity artifacts (credentials, tokens, keys) |
| 5 | Man in the Middle | Interception of communication path |
| 6 | Flooding Attack | Capacity exhaustion through volume/intensity |
| 7 | Malware | Execution of foreign executable content (FEC) |
| 8 | Physical Attack | Physical accessibility to asset (bridge cluster) |
| 9 | Social Engineering | Human psychological susceptibility (bridge cluster) |
| 10 | Supply Chain Attack | Third-party trust dependency (bridge cluster) |
3.2 Key Differentiators: TLCTC vs. ENISA
| Dimension | ENISA Approach | TLCTC Approach |
|---|---|---|
| Classification Basis | Outcome-oriented (ransomware, data breach) | Cause-oriented (generic vulnerability exploited) |
| Mutual Exclusivity | Overlapping categories (double-counting) | Non-overlapping (one step = one cluster) |
| Attack Sequences | Not natively supported | Attack paths: #9→#4→#1→#7 |
| Velocity Analysis | Not addressed | VC-1 to VC-4 classes with Δt notation |
| Bow-Tie Integration | Not present | Core architectural anchor |
| Strategic/Operational | Separate frameworks (ETL + ATT&CK) | Unified dual-layer architecture |
3.3 The Ransomware Example: Classification Comparison
Consider a typical ransomware incident: phishing email → credential theft → lateral movement → data encryption.
ENISA Classification
- Problem: Classified as Ransomware, Malware, Social Engineering, AND Threats Against Data.
- Result: Double-counting of the same incident across multiple categories.
- Missing: No attack sequence visibility.
TLCTC Classification
- Precision: Each step classified by generic vulnerability exploited.
- Clarity: Ransomware is the Outcome (Data Risk Event), #7 Malware is the Cause.
- Velocity: #9→[5m]#4→[2h]#1→[15m]#7
Part IV: How ENISA Would Benefit from TLCTC Integration
4.1 Solving the 'Language Problem'
TLCTC provides the semantic foundation ENISA needs by establishing 10 non-overlapping threat categories based on generic vulnerabilities. This eliminates the classification ambiguity of the current 177-threat taxonomy and separates causes from outcomes via Bow-Tie architecture.
4.2 Enhancing the ETL Methodology
ENISA's ETL reports could integrate TLCTC as a complementary classification layer:
4.3 Improving Risk Assessment Consistency
ENISA's ISO 27005-aligned risk formula (Risk = Impact × Threat Likelihood × Vulnerability Level) would gain precision through TLCTC integration:
- Threat Likelihood: Assessed per TLCTC cluster rather than per outcome category.
- Vulnerability Level: Mapped to generic vulnerabilities (#1-#10) rather than specific CVEs alone.
- Control Effectiveness: Evaluated using attack velocity classes (VC-1 to VC-4).
4.4 Supporting NIS2 and DORA Compliance
The EU's NIS2 Directive and DORA regulation require consistent threat and risk reporting. TLCTC enables standardized incident classification across EU member states, comparable risk registers using cause-based taxonomy, consistent control mapping via TLCTC-to-NIST-CSF integration, and attack path documentation for critical infrastructure sectors.
4.5 Addressing ENISA's 'Under Revision' Taxonomy
Given that ENISA's taxonomy is currently under revision, TLCTC offers a ready-made solution that has been systematically designed rather than organically evolved. It includes axiomatic foundations for consistent interpretation, provides a JSON schema for machine-readable incident documentation, integrates natively with MITRE ATT&CK at the operational layer, and is available under CC BY 4.0 license, aligning with ENISA's open collaboration model.
Conclusion: A Strategic Opportunity
ENISA's cybersecurity frameworks represent the most comprehensive European effort to standardize threat and risk terminology. However, fundamental tensions remain between operational utility and conceptual precision. TLCTC is not proposed as a replacement for ENISA's frameworks, but as a complementary layer that provides the cause-oriented precision currently missing. The integration would strengthen ENISA's position as the EU's cybersecurity authority while addressing the fundamental taxonomic gaps that limit cross-border incident comparability and risk assessment consistency.
| ENISA Gap | TLCTC Solution |
|---|---|
| Outcome-based classification creating double-counting | Cause-based classification with mutual exclusivity |
| No attack sequence capability | Attack path notation (#9→#4→#1→#7) |
| Absent Bow-Tie integration | Bow-Tie as core architectural anchor |
| Implicit domain boundaries | Explicit Domain Boundary Operators |
| Acknowledged 'language problem' | Semantic clarity through axiomatic definitions |
Recommended Next Steps
- Engage ENISA's Threat Landscape team during their taxonomy revision process.
- Propose TLCTC mapping to ETL prime threats as pilot integration.
- Offer TLCTC JSON schema for STIX 2.1 integration compatibility.
- Demonstrate attack path notation value for NIS2/DORA compliance reporting.
References
- ENISA Threat Landscape 2025 (October 2025)
- ENISA CTL Methodology (Updated August 2025)
- ENISA Threat Taxonomy v1.0 (January 2016, updated 2022)
- ENISA Compendium of Risk Management Frameworks (2022)
- ENISA 'Definition of Cybersecurity – Gaps and overlaps in standardisation' (2015)
- ENISA Interoperable EU Risk Management Toolbox (2023)
- ENISA Reference Incident Classification Taxonomy (RSIT)
- Top Level Cyber Threat Clusters (TLCTC) v2.0 White Paper
