The cybersecurity industry is trapped in a pre-paradigmatic state, characterized by semantic diffusion and fragmented terminology. Drawing on the philosophy of science—specifically Kuhn, Popper, Carnap, and Quine—this article argues that technical threats follow scientific principles and that we need a shared foundation, like TLCTC, to turn our craft into a science.
The world of cybersecurity is caught in a strange paradox: we have more tools, more experts, and more budgets than ever before – yet we keep losing ground. The usual answer is that attackers are getting better. But what if the problem runs deeper? What if we don't even know what we're talking about?
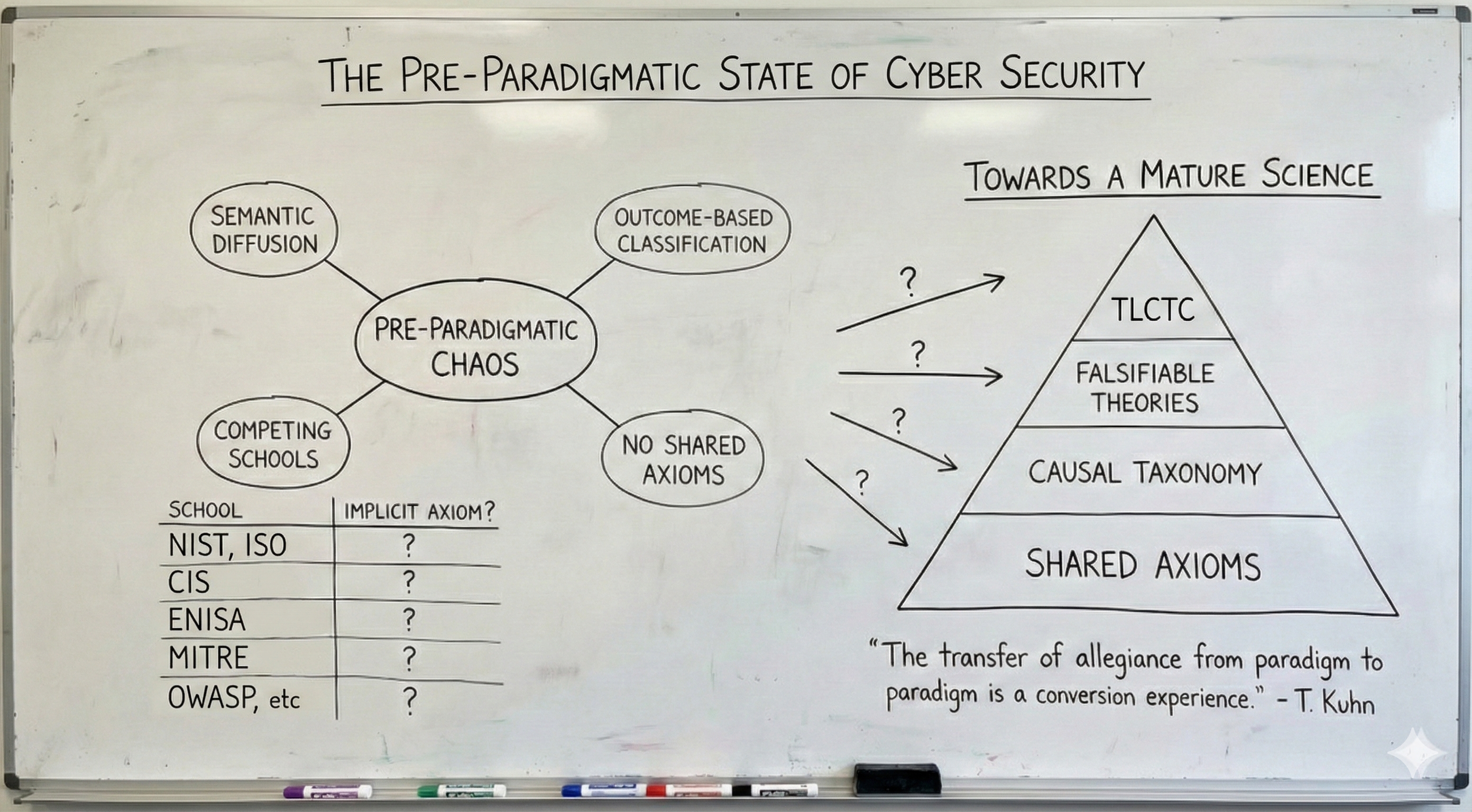
The philosopher of science Thomas Kuhn described a condition in his seminal work The Structure of Scientific Revolutions that captures our situation precisely: the pre-paradigmatic phase. It is the state of a discipline before it becomes a science.
What Does "Pre-Paradigmatic" Mean?
Kuhn observed that young sciences follow a characteristic development. Before the establishment of a first shared paradigm, competing schools exist side by side. Each develops its own terminology, its own methods, its own explanatory models. They observe the same reality – but they cannot compare their observations, cannot combine them, cannot build upon each other's work.
The breakthrough comes not through better instruments or more data. It comes through a shared foundation: axioms, definitions, a language that everyone shares.
Physics before Newton. Chemistry before Lavoisier. Medicine before germ theory. In each of these disciplines, there were brilliant practitioners, useful techniques, partial knowledge. What was missing was the foundation that turns craft into science.
"The transfer of allegiance from paradigm to paradigm is a conversion experience that cannot be forced."
The Symptoms in Cybersecurity
Let's examine the current landscape through this lens:
- Fragmented Terminology: CrowdStrike speaks of "eCrime" and "targeted intrusion." Mandiant categorises by threat actor groups. ENISA uses yet another taxonomy. Verizon structures its DBIR around patterns. They all observe the same attacks on the same digital infrastructure – yet their reports cannot be compared, cannot be merged, cannot be translated into consistent protective measures.
- Semantic Diffusion: What does "threat" mean? What is a "risk"? What exactly constitutes "protection requirements"? Ask ten experts and you'll get twelve answers. Not because the experts are incompetent – but because there are no shared definitions they can reference.
- Control-First Instead of Cause-First: Regulations and standards prescribe controls without naming the threats those controls are meant to protect against. This is like a doctor prescribing medication without ever making a diagnosis. It works sometimes – but it isn't medicine. It's hope.
- The Measurement Problem Behind the Language Problem: We cannot measure what we cannot name. We cannot compare what is defined differently. Every organisation fights alone because we lack a common basis for sharing experience.
Why Technical Threats Follow Scientific Principles
Some might object: cybersecurity isn't a "real" science, not a natural science. But this objection misses something fundamental.
Cyber threats are causal and reproducible. A buffer overflow follows the same principles in Berlin as in Bangalore. SQL injection works according to identical mechanisms regardless of who executes it. Social engineering exploits universal cognitive patterns anchored in human psychology.
These are not random events. They are systematic exploitations of regularities. Where causality reigns, where reproducibility is possible, where predictions can be made – there the rules of scientific inquiry apply.
The question is not whether cybersecurity follows scientific principles. The question is why we have not yet established a shared scientific foundation.
The Scientific Void
"The breakthrough comes not through better instruments or more data. It comes through a shared foundation."
TLCTC: The Missing Foundation
The Top Level Cyber Threat Clusters Framework is an attempt to create this foundation. Not as a replacement for existing frameworks – NIST CSF, ISO 27001, MITRE ATT&CK all do valuable work. But they all presuppose something that was never explicitly defined: a consistent taxonomy of causes.
TLCTC classifies threats by the generic vulnerability they exploit – not by outcomes like "ransomware" or "data breach." Ten clusters. Ten fundamental attack vectors. A structure that can be applied to any environment.
What this enables:
- Comparability: When CrowdStrike and Mandiant and ENISA reference the same clusters, their reports become combinable.
- Precision: "We have a problem with attack path #9→#4→#1" is more actionable than "We have a phishing problem" – because it names the chain, not a specific technique.
- Diagnosis Before Therapy: First identify the threat, then choose the control. The logical sequence that is so rarely followed in practice.
The Invitation
A paradigm doesn't establish itself by decree. It establishes itself by solving problems that previously seemed unsolvable. By enabling communication that was previously impossible. By giving practitioners tools that actually work.
TLCTC is a proposal. A hypothesis. A foundation that wants to be tested.
The anomalies of the current state are obvious: reports that cannot be compared. Standards that prescribe controls without naming threats. Experts talking past each other because they lack a shared language.
The question is not whether we need a shared paradigm. The question is whether we're ready to build one. TLCTC is licensed under CC BY 4.0. Use it, test it, break it – and tell us what's missing.
Addendum: A Brief Stroll Through the Philosophy of Science
Anyone engaging with Kuhn inevitably encounters three other names who shaped our thinking about scientific knowledge. Their perspectives shed additional light on what TLCTC attempts to achieve.
Karl Popper: The Invitation to Refutation
Popper proposed a radical criterion: a theory is only scientific if it is falsifiable. Not confirmation that counts, but the possibility of refutation. A statement compatible with everything says nothing at all.
For TLCTC, this means: the framework makes a testable claim. If it turns out that the ten clusters fail to capture essential threat classes – if anomalies emerge that cannot be classified – then the framework must be adapted or abandoned. This is not a flaw but a mark of quality. "Use it, break it" is essentially Popper's imperative in different words.
Rudolf Carnap: The Longing for Precise Language
Carnap, one of the leading minds of the Vienna Circle, devoted his life to the question: how do we build a language in which misunderstandings become structurally impossible? His answer was formal systems – syntactically exact, semantically unambiguous.
Carnap would have diagnosed cybersecurity's "semantic diffusion" as a symptom of insufficiently formalised language. When "threat" means ten different things in ten different contexts, what's missing isn't expertise – it's a shared grammar. TLCTC is, in a sense, a Carnapian project: the attempt to define foundational terms so they remain stable across contexts. Not out of pedantry, but because precise communication is the precondition for collective action.
Willard Van Orman Quine: No Statement Stands Alone
Quine challenged the idea that individual statements can be verified in isolation. In his "Two Dogmas of Empiricism," he argued: our beliefs form a web. When an experiment fails, we can adjust various nodes in the web – not just the most obvious hypothesis.
For cybersecurity, this is an uncomfortable truth. When an attack succeeds, is it the firewall? The process? The human? The architecture? The answer is almost always: several things at once, in interaction. TLCTC does not attempt to deny this complexity. But it offers a structure for naming the nodes in the web. Only when we know which factors interact can we meaningfully discuss their interrelationships.
Why These Names?
Not to borrow academic authority. But because these thinkers worked on problems we encounter daily in cybersecurity – even if we rarely name them as such:
- How do we distinguish genuine knowledge from pseudo-knowledge? (Popper)
- How do we communicate precisely about complex matters? (Carnap)
- How do we understand systems where everything connects to everything? (Quine)
- How do we establish shared foundations in a fragmented field? (Kuhn)
Cybersecurity has long ignored these questions. Perhaps it's time to ask them.
References & Further Reading
- Kuhn, T. S. The Structure of Scientific Revolutions. University of Chicago Press, 1962.
- Popper, K. The Logic of Scientific Discovery. Routledge, 1959.
- Kreinz, B. Top Level Cyber Threat Clusters (TLCTC), White Paper V2.0
- Carnap, R. The Logical Syntax of Language. 1934.
