Most cybersecurity investments fail because organizations haven't answered a fundamental question: "How much of this threat are we willing to accept?" This article presents a structured approach to fixing that problem by anchoring risk appetite to three specific asset scopes and using the 10 TLCTC clusters as the negotiation language.
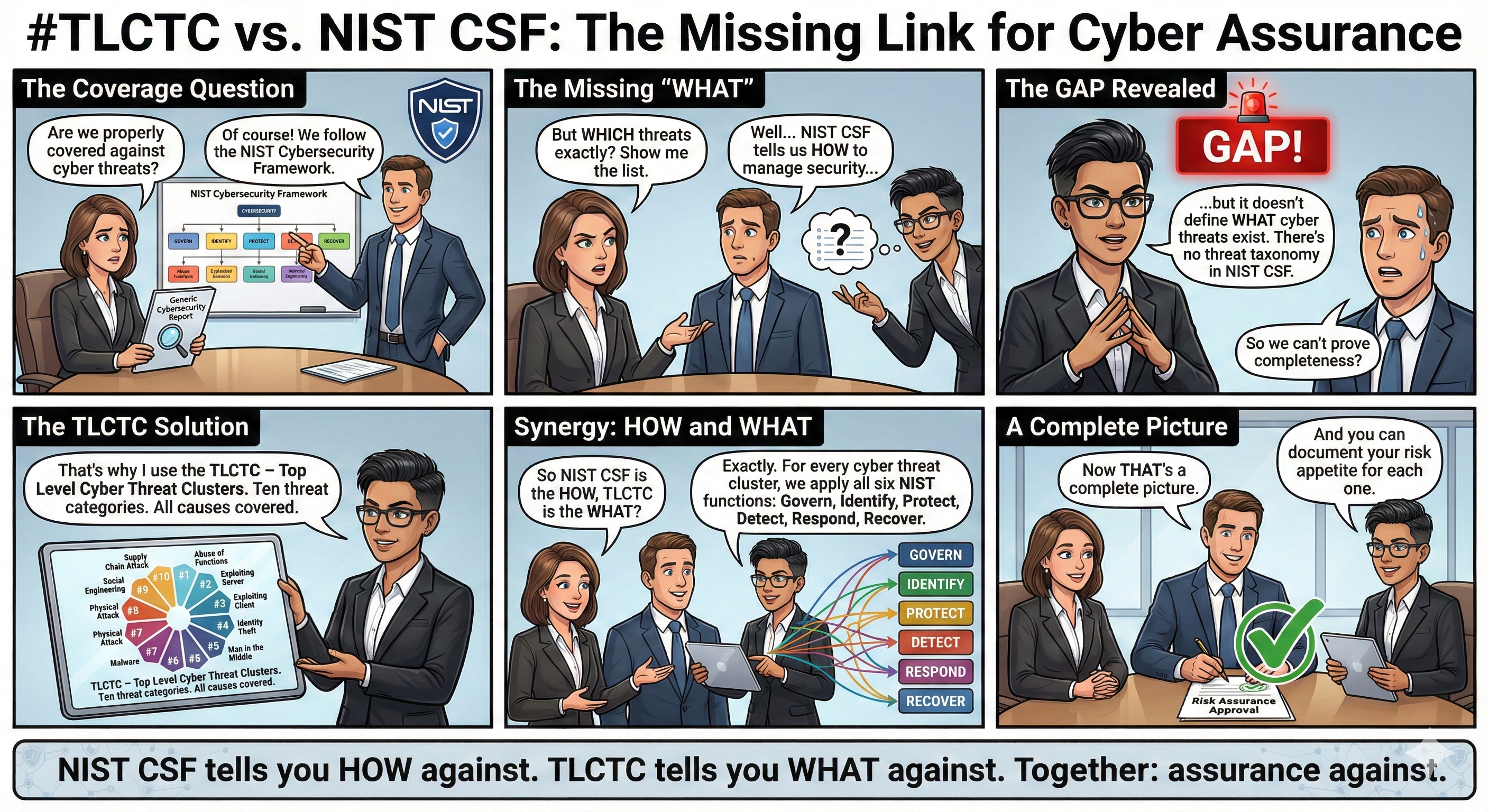
Most cybersecurity investments fail not because of technology, but because nobody answered a fundamental question: How much of this threat are we willing to accept?
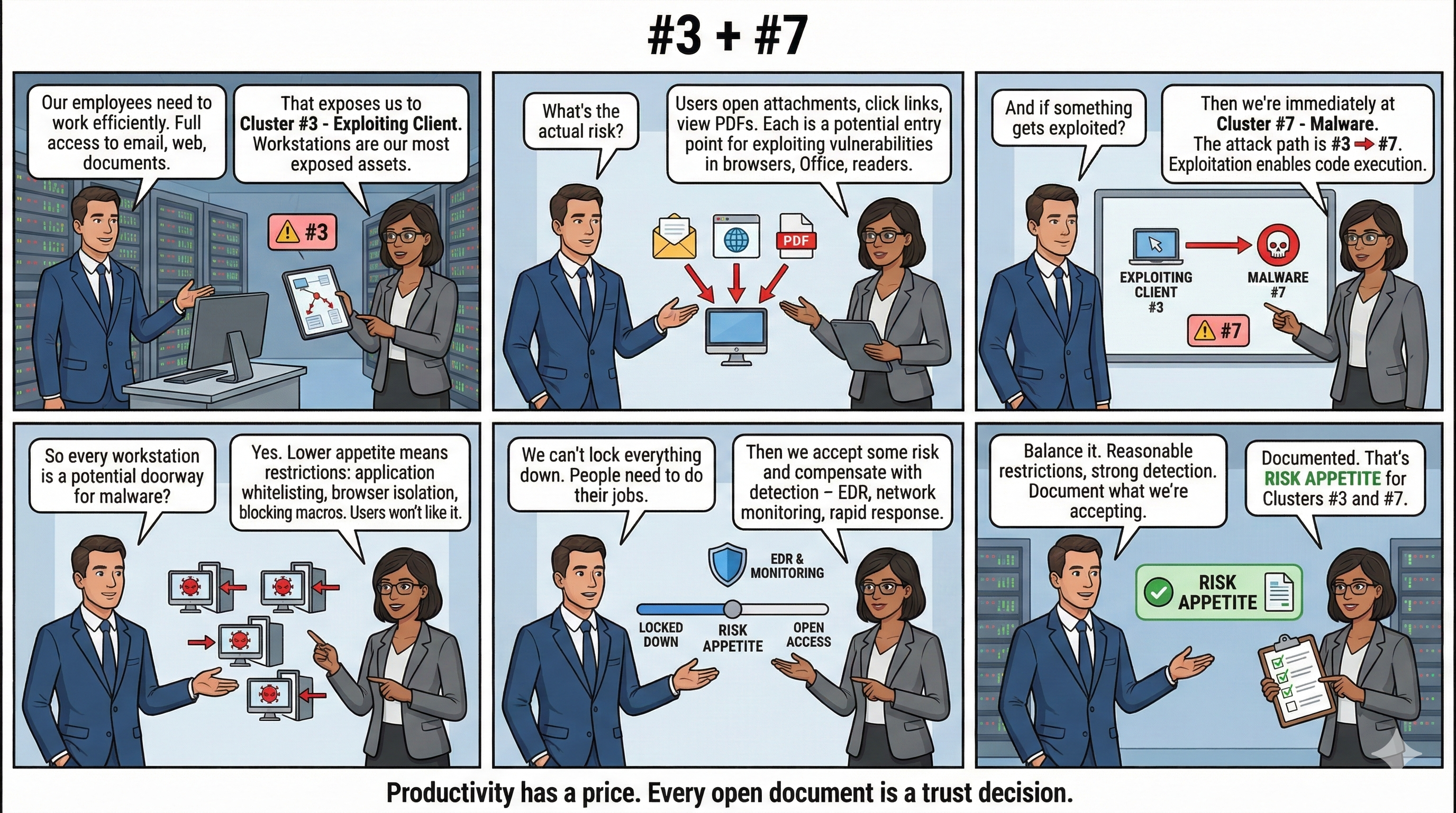
Without that answer, security teams operate in a vacuum. Controls get implemented without explicit business mandate. Budgets get approved without clear accountability. And when incidents inevitably occur, the finger-pointing begins—because no one ever agreed on what level of risk was acceptable in the first place.
This article presents a structured approach to fixing that problem. It requires three conversations, each anchored to a different asset scope, and it starts not with security—but with business strategy.
The CISO's Opening Move
A good CISO doesn't begin with threats, vulnerabilities, or compliance frameworks. They begin with a simple question to the executive team:
"What are we trying to achieve as a business?"
From that answer, the CISO identifies which assets are exposed—and to what. Only then can a meaningful risk appetite discussion take place.
The method is straightforward: for each asset scope, the CISO presents all ten categories of cyber threat and proposes the lowest possible appetite as the default position. This isn't obstruction. It's an invitation to negotiate.
Why start with lowest appetite? Because it forces the business to explicitly state where tolerance exists. Every deviation from "zero tolerance" becomes a documented business decision—owned by executives, not IT.
Three Conversations, Three Asset Scopes
Cyber risk appetite cannot be set once for the entire organization. Different assets serve different purposes and carry different risk profiles. A comprehensive approach requires three separate conversations:
-
Conversation 1: Customer-Facing Assets (e-Channels)
Owned by: CEO, CDO, Business Leadership
Focus: Digital services, customer portals, mobile apps, onboarding systems -
Conversation 2: Internal Process Assets
Owned by: CIO, COO
Focus: Operational systems, employee access, privileged identities, core infrastructure -
Conversation 3: Third-Party and Supply Chain
Owned by: CPO, Legal, CIO
Focus: Vendor relationships, outsourced services, software dependencies, update mechanisms
For each conversation, the executive team must set appetite levels across all ten threat categories. The same threat cluster may warrant different tolerances depending on the asset scope. That's not inconsistency—that's strategy.
A Worked Example: e-Channel Strategy
Consider an organization with the following business objectives:
- Enlarge the user base through easy onboarding processes
- Enable 24/7 digital service availability
- Ensure users feel secure when using e-solutions
- Maintain a strong reputation regarding IT services
Supporting these objectives, the IT strategy includes centralized customer identity management, user-friendly onboarding, and high-availability monitoring.
Now the CISO enters the conversation—not to block these objectives, but to quantify the risk they create. Using the ten threat clusters as a structured vocabulary, the discussion might unfold as follows:
Cluster #4: Identity Theft (Account Exploitation)
The business wants easy onboarding. Easy onboarding means lower friction. Lower friction typically means weaker initial authentication.
- The CISO's default position: Zero tolerance for identity theft.
- The business response: That would require step-up authentication from day one, which kills conversion rates. We need some tolerance here.
- Qualitative statement: We accept that some account compromises will occur due to our onboarding design.
- Quantitative boundary: Maximum n identity theft incidents per month, with cash-out losses not exceeding €X per month.
- Architectural implication: Implement progressive trust—new accounts start with limited functionality; higher privileges require stronger verification.
- Accountability: Business owns the fraud loss within tolerance; Security owns detection and response.
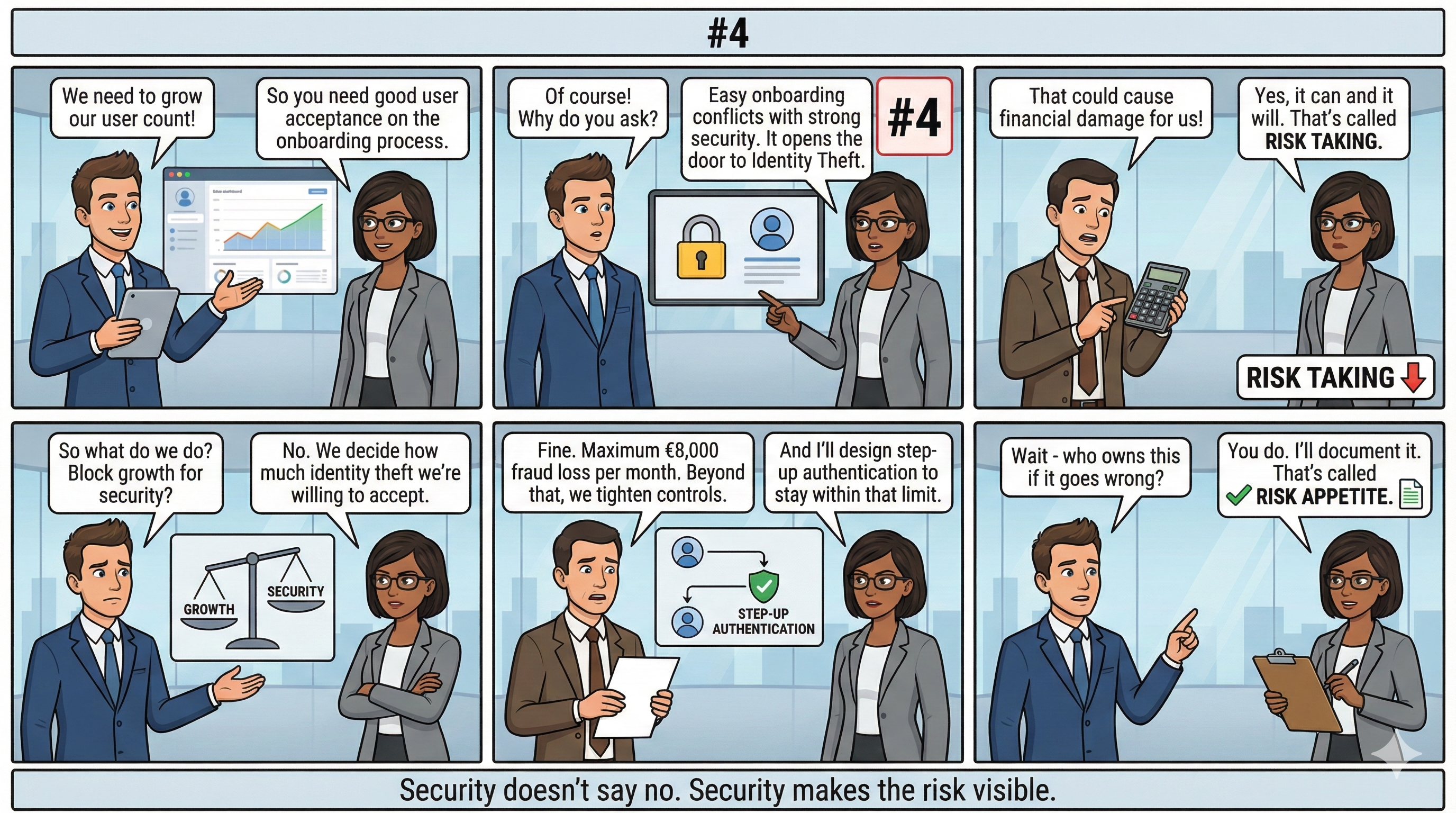
This is a fundamentally different conversation than "implement MFA." It connects a specific threat to a specific business objective and produces a measurable boundary that both sides can be held to.
Cluster #2: Exploiting Server
The business objective includes reputation protection — we and users must feel secure.
- The CISO's default position: Zero tolerance for Exploits in our e-Channels.
- The business response: Agreed. Reputation damage from a breach would undermine everything we're building.
- Qualitative statement: We have low risk appetite for data breaches and will not accept reputation damage from server exploits.
- Operational authority: In the event of confirmed compromise activity, Security has authority to shut down affected services—even if this violates availability SLAs.
- Accountability: This is the one area where security overrules business continuity.
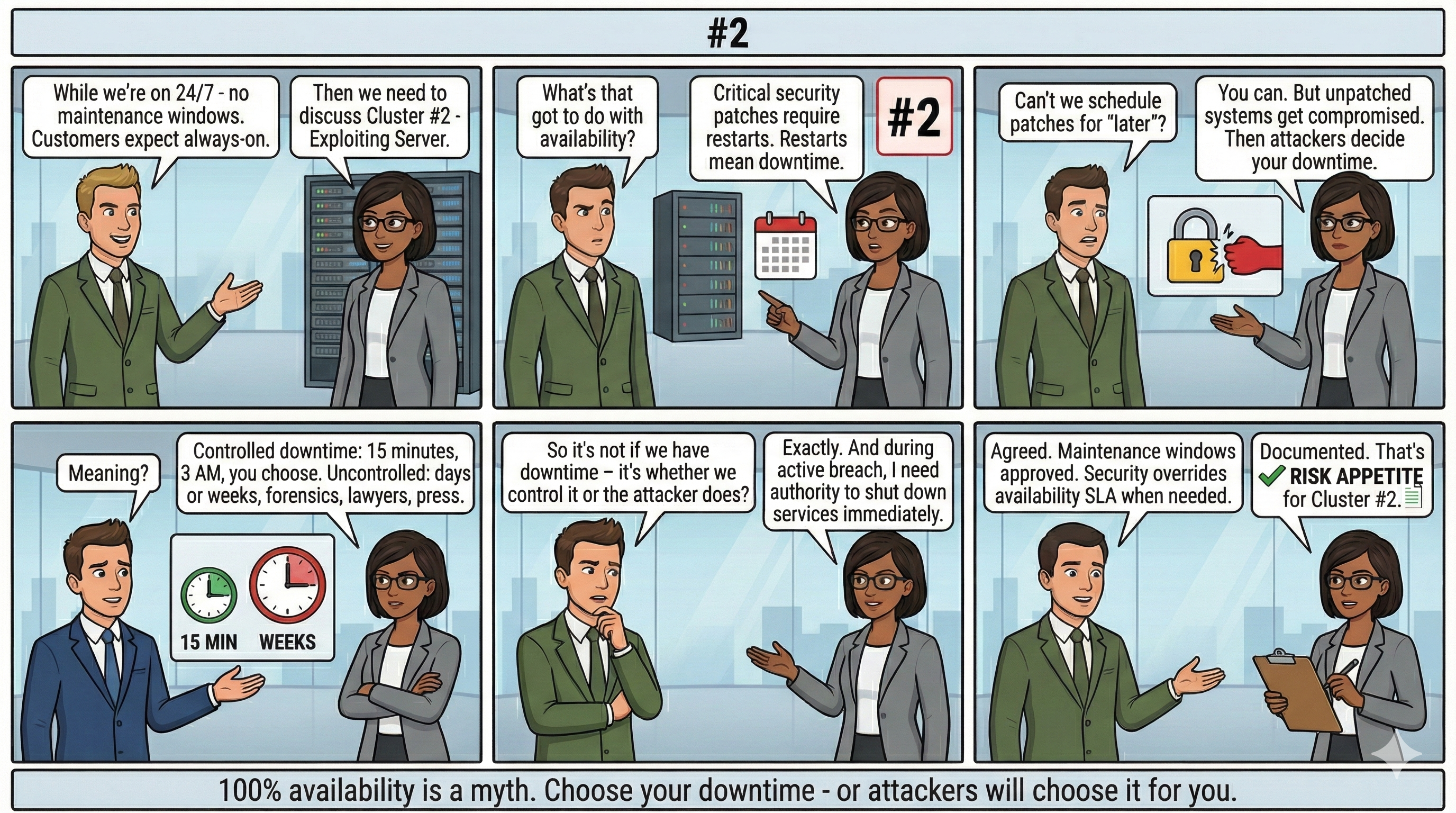
Notice what happened: the business agreed with the CISO's default position. The conversation still mattered—because now that agreement is explicit and documented.
Cluster #6: Denial of Service (Flooding Attack)
The business wants 24/7 availability for internet-facing services.
- The CISO's default position: Zero tolerance for service disruption.
- The business response: We want that too. What does it cost?
- The CISO's answer: True zero tolerance for DoS on internet-facing services requires external protection—CDN providers, DDoS mitigation services, redundant infrastructure. That's a significant budget line.
- Qualitative statement: We accept that some DoS exposure is inherent to operating public services.
- Quantitative boundary: Services should withstand attacks up to X Gbps; beyond that, degradation is accepted.
- Budget decision: The lower the appetite, the higher the investment. Business must fund the protection level they declare.
- Accountability: CFO approves the protection budget; Security implements to that specification.

Here the conversation reveals a cost feedback loop. Risk appetite isn't just a policy statement—it's a budget allocation.
Why This Works
This approach produces several outcomes that traditional security planning does not:
- Threat clusters become executive vocabulary. Instead of discussing "vulnerabilities" or "attack vectors" in technical terms, leadership can ask: "What's our appetite for Cluster #4?" The ten clusters provide a stable, non-overlapping language for risk discussions.
- Appetite drives architecture. The "step-up onboarding" design isn't a technical preference—it's a direct implementation of the risk tolerance statement for identity theft. Security architecture becomes traceable to business decisions.
- Cost accountability is clear. When the business declares low appetite for DoS but won't fund external protection, that contradiction is visible. The CISO has documentation; the CFO has a decision to make.
- Control hierarchies emerge naturally. The example shows that data breach (#2) can override availability SLAs, while identity theft (#4) operates within managed loss boundaries. These aren't arbitrary—they flow from the risk appetite statements.
Extending the Model
The e-Channel example above is one of three required conversations. The same structure applies to internal assets and third-party relationships, though the appetite levels will differ.
For internal process assets, Cluster #4 (Identity Theft) likely returns to zero tolerance—because privileged identities with administrative access cannot operate under "managed fraud loss" assumptions. The same cluster, different scope, different appetite.
For third-party and supply chain assets, Cluster #10 (Supply Chain Attack) becomes central. Every vendor relationship inherits exposure to all ten clusters. The question becomes: what tolerance do we have for risks that originate outside our direct control?
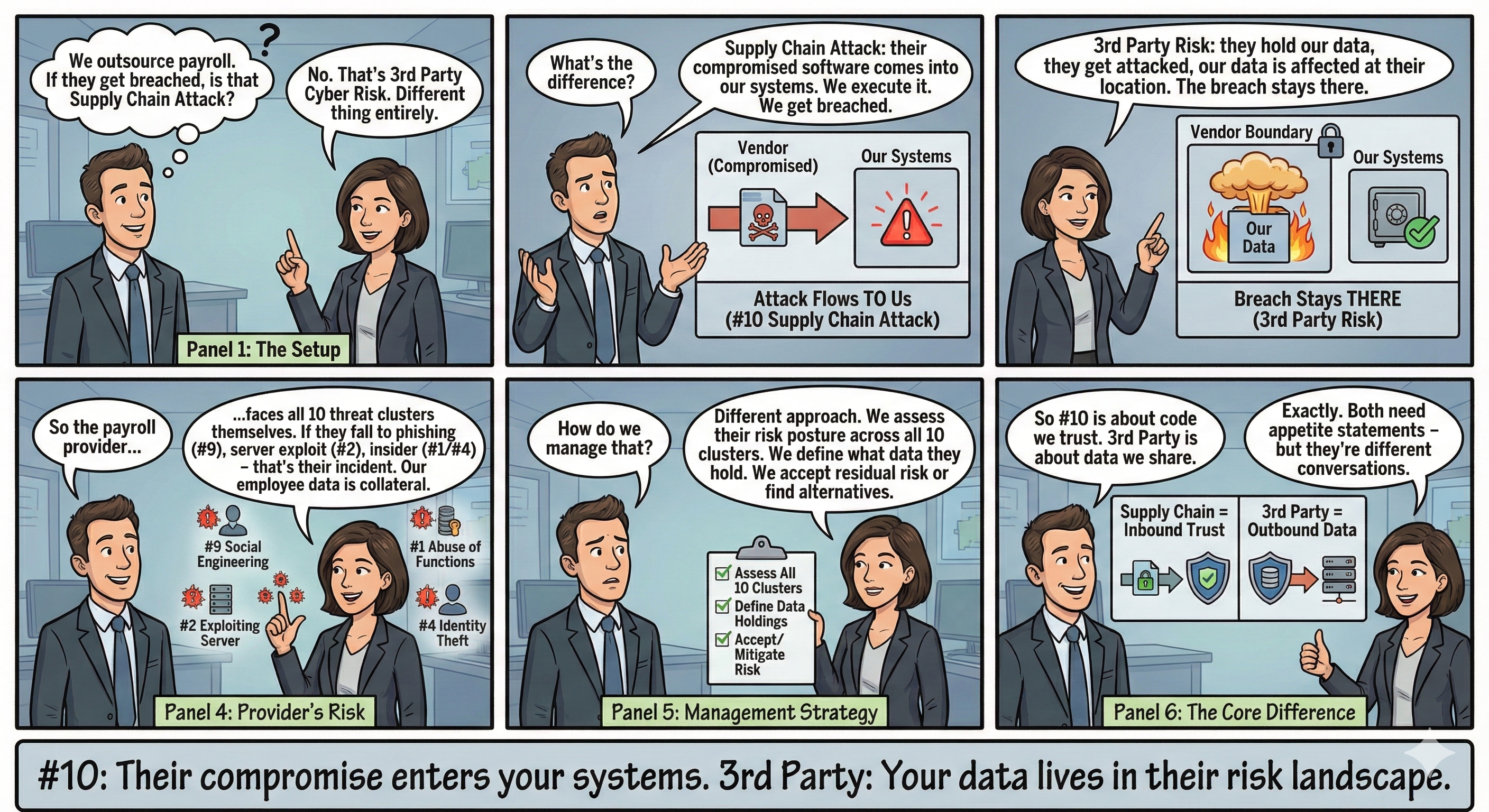
A complete cyber risk appetite framework documents all three scopes, all ten clusters, with explicit qualitative and quantitative statements for each cell in that matrix.
The CISO as Strategic Partner
This model repositions the CISO from "the person who says no" to "the person who structures the conversation."
By starting with business strategy, anchoring to asset scopes, and using threat clusters as a shared vocabulary, the CISO enables executives to make informed risk decisions—and to own those decisions explicitly.
The default position of lowest appetite isn't adversarial. It's a negotiation tactic that ensures every tolerance statement is conscious, documented, and attributable.
When the next incident occurs—and it will—the organization won't be asking "who's responsible?" They'll be asking "did we stay within our stated tolerance?" That's a fundamentally different conversation, and a fundamentally healthier organization.
The ten threat clusters referenced in this article are defined in the TLCTC (Top Level Cyber Threat Clusters) framework, a cause-oriented taxonomy for cyber risk assessment. For the complete framework, visit tlctc.net.
References
- Kreinz, B. Top Level Cyber Threat Clusters (TLCTC), White Paper V2.0
