The National Institute of Standards and Technology (NIST) provides authoritative definitions and frameworks for managing cyber risk, but intentionally focuses on the process of risk management rather than providing a structured, universally adopted taxonomy of cyber threats based on root causes. This distinction has significant structural consequences for cybersecurity risk management practices across organizations.
1. NIST's Foundational Definitions: Process-Oriented
NIST defines both cyber risk and cyber threats, anchoring them in the context of adverse outcomes and the framework for assessing them, particularly within NIST Special Publication (SP) 800-30 and the Cybersecurity Framework (CSF).
Cybersecurity Risk (The Consequence): Defined as "An effect of uncertainty on or within information and technology". This risk is directly tied to the potential loss of Confidentiality, Integrity, or Availability (CIA) of information or systems. Risk reflects the potential adverse impacts to organizational operations (mission, reputation) and assets, individuals, other organizations, and the Nation. Fundamentally, Risk is a function of Threat, Vulnerability, and Impact.
Cyber Threat (The Cause/Event): Defined as "any circumstance or event with the potential to adversely impact organizational operations... through an information system via unauthorized access, destruction, disclosure, modification of information, and/or denial of service". In the risk process, a threat is characterized as the potential for a threat-source to exercise (exploit) a specific vulnerability. Threat Sources include adversarial (e.g., cybercriminals, insiders), accidental (e.g., user error), structural (e.g., equipment failure), and environmental (e.g., natural disasters).
2. The Structural Gap: Event-Centricity, Not Taxonomy
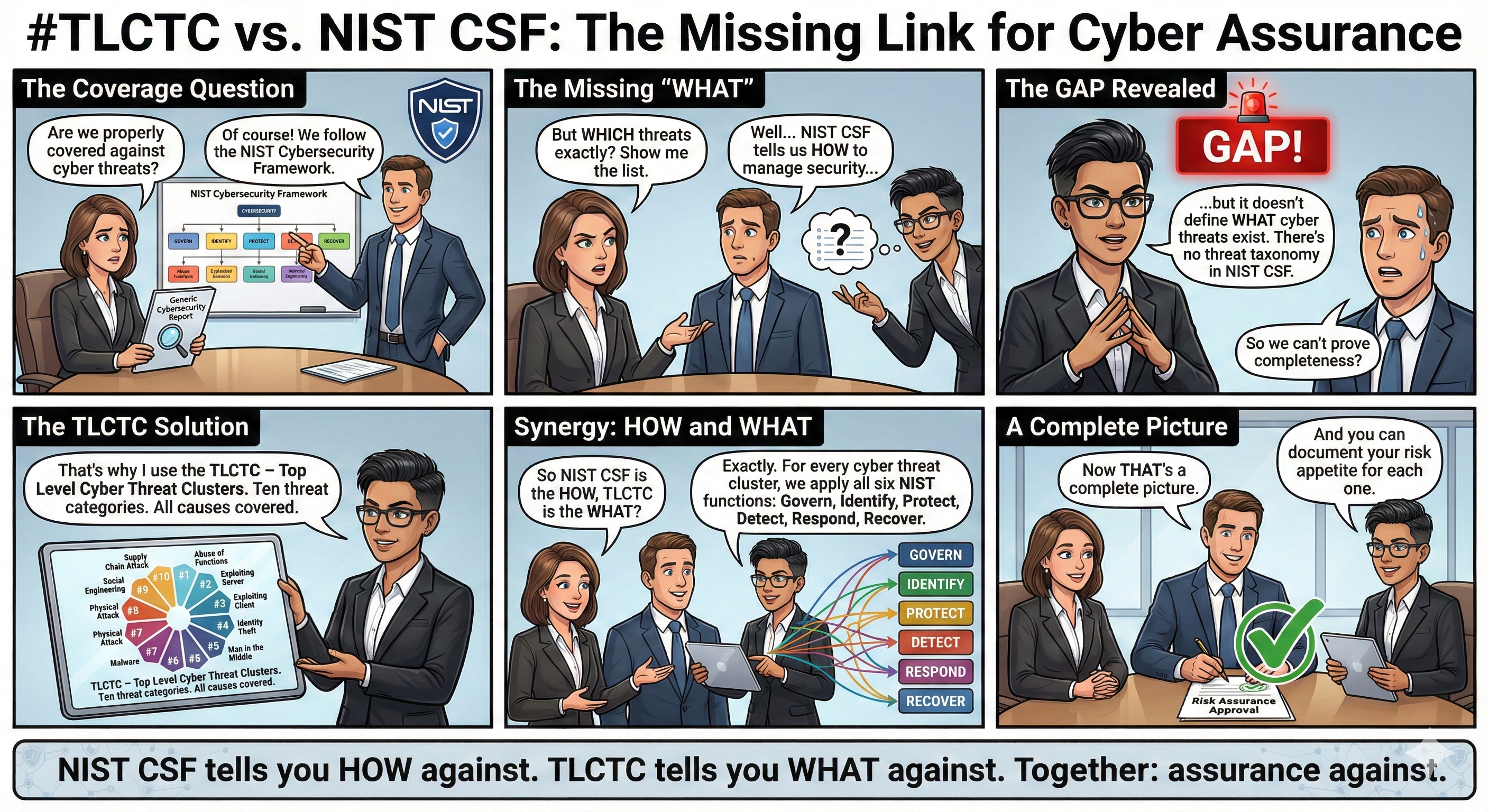
The core limitation identified in global standards regarding NIST is that while it mandates the identification of threats, it does not provide a standard categorization structure for those threats.
Event-Centric Focus: The NIST SP 800-30 definition focuses on the "circumstance or event" that can cause harm. This approach is often criticized for lacking structural clarity between a threat's cause, event, and consequence, making it difficult to categorize cyber threats distinctly.
Mandate for External Input: The NIST risk assessment process (detailed in SP 800-30 Rev. 1) mandates identifying potential threats and vulnerabilities (Task 2-2/Step 3). However, the framework intentionally relies on external or organization-specific taxonomies for this critical input data, as confirmed by its documentation.
Focus on Outcomes: The NIST Cybersecurity Framework (CSF) 2.0 focuses on high-level cybersecurity outcomes categorized under six Functions (GOVERN, IDENTIFY, PROTECT, DETECT, RESPOND, RECOVER). The CSF defines the control placement and program architecture, but does not provide a structured, cause-oriented threat taxonomy. The ability to effectively "Protect" depends on having first identified the specific threat mechanisms, which the CSF does not categorize.
3. Consequences for Risk Management and Integration
The lack of a standardized, cause-oriented threat classification structure directly results in fragmentation and inefficiency across the security ecosystem.
- Inconsistent Reporting: Variability in how organizations define and classify threats is a major source of inconsistent risk reporting. Without a common language, comparing and aggregating cyber risk across industries and borders becomes challenging.
- Scaling Challenges: NIST SP 800-30 uses a threat-based model (Threat Source → Threat Event → Vulnerability → Predisposing Conditions → Impact), which is difficult to scale because it requires complex, time-consuming threat-event mapping for every system.
- Misaligned Strategy: The semantic blur caused by mixing threats, vulnerabilities, events, and consequences hinders effective strategic defense planning. When strategic decisions are based on symptoms or consequences (like "Ransomware" reports), resources may be misallocated toward symptom control rather than upstream prevention of the initial causal mechanisms.
- Compliance Complexity: New, prescriptive regulations (like the EU's DORA and NIS2 Directive) demand consistent threat terminology for incident reporting and risk management, highlighting the urgent need for a unified taxonomy that NIST currently does not provide.
4. Addressing the Gap: The Need for a Cause-Oriented Taxonomy
The fragmented nature of the landscape has led to the development of complementary frameworks designed to supply the missing taxonomical structure needed to feed NIST's process models accurately.
- TLCTC as the Missing Layer (L1): The Top Level Cyber Threat Clusters (TLCTC) framework aims to act as the unifying semantic layer—a "Rosetta Stone"—by providing a stable, logically derived, cause-oriented taxonomy of 10 fundamental attack mechanisms.
- Bridging Frameworks: TLCTC resolves the gap by providing the Taxonomy Layer (L1) needed to connect NIST's Strategic Layer (L0) (e.g., CSF Functions) with operational models like MITRE ATT&CK (the Operational Layer, L2).
- Integration with CSF: By mapping the 10 threat clusters to the six NIST CSF Functions (GOVERN, IDENTIFY, PROTECT, DETECT, RESPOND, RECOVER), organizations can establish specific control objectives for each threat cluster, enabling targeted risk mitigation that the current NIST definitions alone cannot easily support. This enhances the strategic risk register, ensuring all major categories of cyber threats are considered consistently.
- Focus on Root Cause: This complementary approach allows organizations to shift the strategic focus from addressing the consequence (e.g., Ransomware) to preventing the root cause (e.g., #9 Social Engineering or #2 Exploiting Server), which leads to more effective resource allocation and prevention strategies.
Licensed under Creative Commons Attribution 4.0 International (CC BY 4.0).
