Cybersecurity has a language problem. We use "threat" to mean a dozen different things. This isn't just semantics; it blocks effective risk management. TLCTC provides a universal solution.
The Problem
Cybersecurity has a language problem.
We use "threat" to mean a dozen different things: the attacker, the vulnerability, the malware, the breach, the ransomware demand. When a CISO briefs the board, when a SOC analyst writes an incident report, when a vendor sells a solution—they're often using the same words to describe fundamentally different things.
This isn't just semantics. It means we can't compare incidents. We can't aggregate threat intelligence cleanly. We can't map controls to threats with confidence. And we can't communicate risk consistently across teams.
The Solution
TLCTC (Top Level Cyber Threat Clusters) is a cause-oriented taxonomy that classifies cyber attacks by how they happen—the generic vulnerability they exploit—not by who's attacking, what tools they use, or what the outcome is.
Ten clusters. Non-overlapping. Universal across any technology environment.
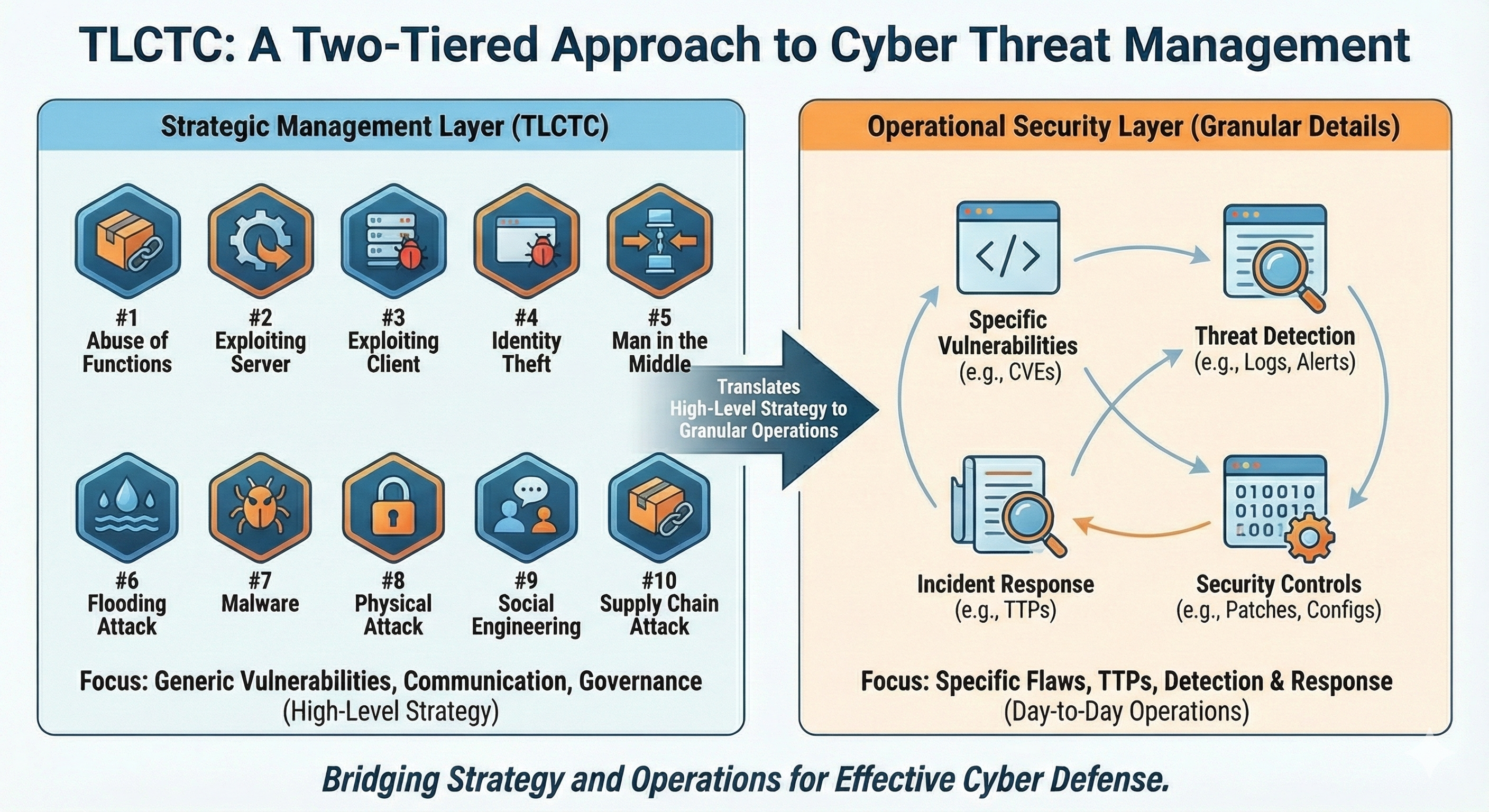
| #Cluster | What It Means |
|---|---|
| #1 | Abuse of Functions Misusing legitimate features—no code flaw required |
| #2 | Exploiting Server Triggering a bug in software that accepts requests |
| #3 | Exploiting Client Triggering a bug in software that consumes content |
| #4 | Identity Theft Using someone else's credentials to authenticate |
| #5 | Man in the Middle Intercepting or manipulating communications in transit |
| #6 | Flooding Attack Overwhelming capacity to cause disruption |
| #7 | Malware Execution Executing foreign code through normal execution paths |
| #8 | Physical Attack Unauthorized physical access or interference |
| #9 | Social Engineering Manipulating humans into acting against security |
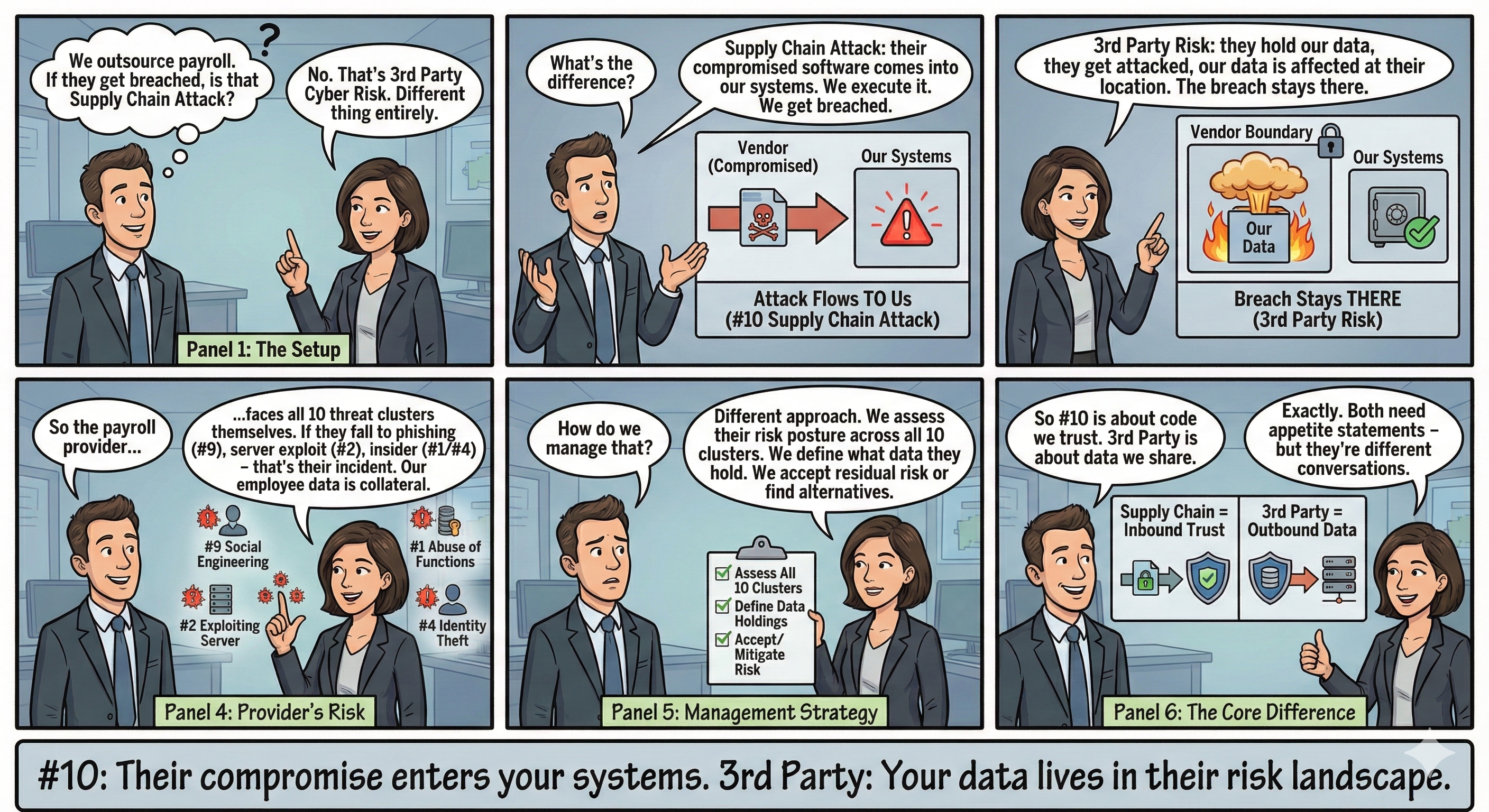
| #10 | Supply Chain Attack Exploiting trusted third-party relationships |
Why This Matters
Ransomware isn't a threat category—it's an outcome.
When we say "ransomware attack," we're describing the result (encrypted files, extortion demand) and maybe the tool. But the actual threat path might look like this:
#9 Social Engineering → #7 Malware → #4 Identity Theft → (#1 Abuse of Functions + #7 Malware)
→ [Data Encryption - Loss of Availablility]A phishing email tricks someone into running malware. The malware harvests credentials. Those credentials access legitimate admin tools. Data gets encrypted.
Each step exploits a different generic vulnerability. Each step has different controls. Calling the whole thing "a ransomware attack" obscures what actually happened—and what could have stopped it.
TLCTC gives you the grammar to describe this precisely.
The Key Insight: Causes vs. Consequences
TLCTC is built on the Bow-Tie risk model, which enforces a strict separation:
- Left side (causes): How did the attacker get in? → TLCTC clusters live here
- Center: Loss of Control—the moment the attacker succeeds
- Right side (consequences): What happened next? → Data breach, service outage, fraud
This separation matters because:
- The same threat path can lead to different consequences
- The same consequence can result from different threat paths
- Controls on the cause side prevent; controls on the consequence side contain
When you conflate cause and effect, you can't reason clearly about either.
What You Can Do With It
- Compare incidents — Express any intrusion as a chain of cluster steps, making incidents directly comparable regardless of technology or sector.
- Map controls precisely — Each cluster represents a distinct attack surface. Map your controls to specific clusters instead of vague threat categories.
- Measure what matters — Track attack velocity (how fast attackers move between steps) against your detection speed. Know where you're structurally too slow.
- Communicate clearly — Give leadership, risk, and technical teams a shared vocabulary that means the same thing to everyone.
Go Deeper
TLCTC v2.0 includes:
- Ten foundational axioms that constrain interpretation and ensure consistent classification
- Classification rules (R-Rules) for handling common ambiguities
- Attack Path notation with velocity (Δt) and topology dimensions
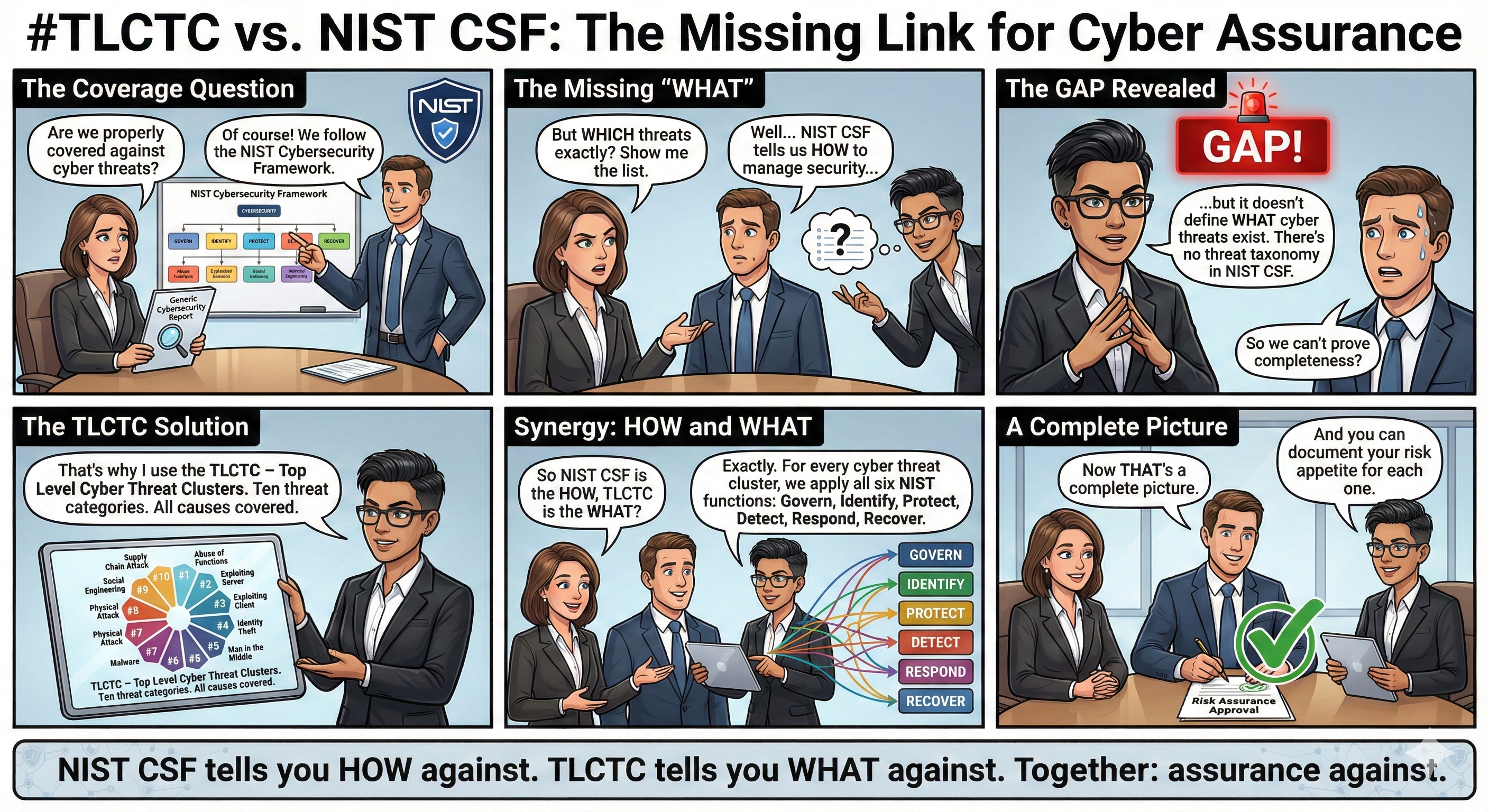
- Control framework integration mapping clusters to NIST CSF functions
- Machine-readable JSON schemas for automation and tooling
TLCTC is designed to be a translation layer—connecting risk management, security operations, and executive communication through a shared, precise language for cyber threats.
